The cybersecurity incident that has left Elgin County’s website and email system down since the start of the month may have been the result of a ransomware attack involving a notorious Russia-based ransomware syndicate, Global News has learned.

A cyber threat expert says data purporting to belong to the county was posted to the website of the ransomware group Conti on Monday, possibly shedding new light on the “technical disruption” that has been plaguing the county for the last several weeks.
County officials have been tight-lipped about the source of the disruption, and have provided little in the way of detail to the public about the ongoing problems, including whether any county data may have been breached.
“Since April 1, the county has experienced a technical disruption that has restricted our ability to communicate via email with external contacts. This disruption has also resulted in the shut down of our website,” said Mary French, Elgin County’s warden, during a county council meeting on Tuesday.
“Our team continues to work tirelessly to restore functionality and is hopeful that we’ll be able to achieve a full restore of our systems sometime this week. We sincerely apologize for the inconvenience this has caused.”
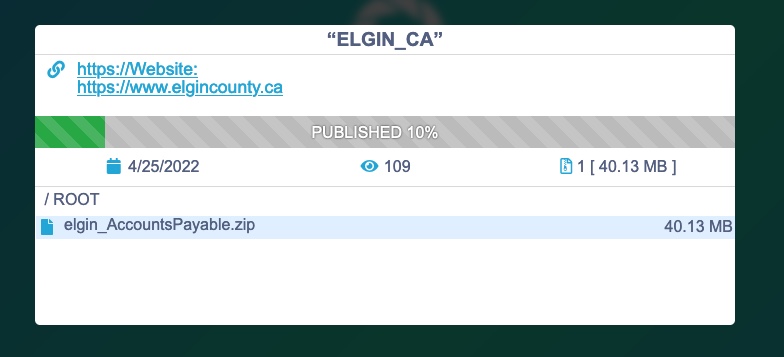
The data purportedly posted to the Conti portal included at least one 40 megabyte ZIP file labelled “elgin_AccountsPayable.” It appears the listing had been removed by the time Global News accessed the portal late Tuesday morning. The apparent listing indicated that 10 per cent of the purported data had been published. It’s not clear from the purported listing what data Conti may claim to have.
“When groups delist stolen data, as appears to have happened here, it can mean a number of things, including that the target organization’s paid, or that it has agreed to come to the negotiating table,” said Brett Callow, a Vancouver Island-based threat analyst with cybersecurity firm Emsisoft.
“There are, of course, other possible explanations, too.”
Global News was not able to independently verify the authenticity of the Conti listing or the data allegedly posted as it appeared to have already been removed, however Callow says he is not aware of any instance in the past whereby the group has falsely claimed to have stolen data from an organization.
“But, of course, they are criminals, and there’s a first time for everything,” he said.

Get breaking National news
Global News contacted several people involved with the county inquiring about the cybersecurity issues, including French and the county’s chief administrative officer, Julie Gonyou.
“We are aware of the claim that there has been data leaked on a dark web site, and are in the process of investigating this matter further. We have no further comments at this time,” Gonyou, said in an email.
Asked in a follow-up whether any county data had been breached, whether Conti ransomware was involved, and if so, whether the county had agreed to pay a ransom or negotiate, Gonyou reiterated her earlier statement.
County officials first confirmed that a “cyber security incident” had occurred in a memo which was circulated to staff on March 31.
In the memo, later obtained by the London Free Press, Gonyou wrote that the incident had seen a large amount of spam containing malicious attachments or links being sent to staff members. The memo added that an external consultant had been hired to look into the incident and monitor for data breaches.
On Monday, Elgin and the Municipality of Central Elgin issued a joint alert to the public, warning that malicious emails had been circulating that claimed to be from the county and municipality.
Callow said it wasn’t likely that the county was targeted by the group for any particular reason, noting that an overwhelming majority of ransomware attacks are done at random via malicious links in phishing emails or unpatched vulnerabilities on internet-facing networks.
“Ransomware groups like Conti used to simply lock their target systems and demand payments for a key to unlock them. They still do that, but they also steal a copy of the data now which provides them with additional leverage,” Callow said, a tactic known as “double extortion.”
“Should the target organization not pay, they threaten to leak the data online.”
- Opponents focus on Ford’s question period attendance as legislature rises for summer
- Doug Ford denies dissension in PC party after firing of caucus chair over pensions, jet fiasco
- B.C. bars, restaurants welcome change to province’s liquor policy
- Calgary lost 23% of its treated water last year to leaks. What’s the plan to fix it?
Read more: March 21: Ontario security company uncovers ransomware gang affiliate pledging allegiance to Russia
According to the Canadian Centre for Cyber Security, Conti is considered “one of the most sophisticated ransomware groups in operation,” and frequently targets hospitals, governments, medical networks and other critical services.
The ransomware is most commonly distributed through spear-phishing emails which contain malicious attachments or links — emails which are personalized for the recipient to appear more convincing.
“Often the malicious attachment appears to be a regular file type, such as Word, Excel or PDF, but when the victim opens it, malware, such as TrickBot, IcedID, or BazarLoader, downloads and executes on their device,” the agency’s website states.
From there, Conti will often install software called Cobalt Strike, and exploit vulnerabilities to gain persistent access on the network, obtaining credentials and escalating privileges undetected, spreading the infection to all connected devices, the agency says.

Conti typically rents out its ransomware infrastructure to “affiliates” who pay for the service.
A year ago, a Conti ransomware attack forced Ireland’s health system to shut down its information technology system, cancelling appointments, treatments and surgeries.
Last month, Conti pledged its services in support of Russia’s invasion of Ukraine. The move angered cybercriminals sympathetic to Ukraine. It also prompted a security researcher who had long been surveilling Conti to leak a massive trove of internal communications among some Conti operators.
Recently, the group has been named in ransomware attacks involving Panasonic’s Canadian operations, and has also claimed responsibility for a ransomware attack on the computer systems of the Costa Rican government.
Read more: Tips to protect against ransomware attacks
In the case of Elgin County, that a single ZIP file appears to have been posted and then removed, “may well be similar to a kidnapper sending a pinky finger,” Callow said.
“It’s proof that they have the data and are willing to publish it. Groups often start by publishing small amounts of data, and if that isn’t enough to get the target to pay up, they gradually publish more and more.”
Even if the target organization pays the demand, verifying that the ransomware group has actually destroyed the data it collected is all but impossible. Callow notes it’s hard to estimate how many organizations actually do pay up, but says the best guess is likely around 25 per cent.
Earlier this year, the U.S. Cybersecurity and Infrastructure Security Agency said attacks involving Conti ransomware against U.S. and international organizations had risen to more than 1,000.
— with files from The Associated Press












Comments
Comments closed.
Due to the sensitive and/or legal subject matter of some of the content on globalnews.ca, we reserve the ability to disable comments from time to time.
Please see our Commenting Policy for more.