If you thought your fingerprint was unique, think again.

There are actually many similarities across human fingerprint patterns, something researchers say could be exploited by hackers to break into your phone.
WATCH: Apple applies for fingerprint patent
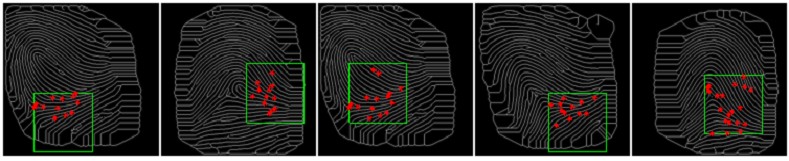
A new report suggests that hackers could potentially use partial prints to fool the fingerprint security system on mobile devices. These partial prints would theoretically be able to unlock the smartphones of those individuals whose fingerprints contain matching patterns. Researchers have dubbed this print the “master print.”
It reveals that the fingerprint-based authentication systems in smartphones use small sensors that do not capture the entire fingerprint. Instead, they scan and store partial fingerprints. Furthermore, many phones allow users to store more than one of their fingerprints on their device, and identity is confirmed when a fingerprint matches any of the stored fingerprints.
This means that fragments from multiple different fingerprints can be used to create a synthetic partial print to unlock many devices.
Fingerprint sensors are a form of biometric authentication, which allows people to use their own bodily traits to sign into their devices. Also included under the umbrella of biometrics are facial recognition and retina scans.
The study’s co-author, professor Nasir Memon of New York University, said in an interview that hackers could potentially take fragments from multiple different fingerprints to create a synthetic partial print that could be expected to unlock many devices.
When his team culled images of fingerprints to create a synthetic partial print, they reported matching of between 26 and 65 per cent of users.
“I was very surprised. When the idea occurred to me to explore it, the numbers were very surprising,” Memon said. He added that while running tests with his lab students, he ordered the results to be double checked because the matches were so high.
While Memon doesn’t believe fingerprint sensors should be removed from the sign-in process entirely, he warns that they may not be the most reliable method to use on their own. “I think fingerprints are very conveniently placed on phones, but they’re more of a visibility feature rather than a security keeper,” he continues.
The iPhone 5s popularized the fingerprint scanner in 2013, and it has appeared in multiple mobile devices since then. Individuals who rely on their device’s fingerprint scanners must first let their device memorize their prints.
On an iPhone, this process involves (after navigating to the Settings page and scrolling down to the Touch ID option) tapping the screen repeatedly to let the device recognize the nuances of the fingerprint. When that’s complete, the user will receive a prompt to alter the position of their finger (likely their second finger or their thumb) and repeat the process until the device has memorized that angle as well.
On Android phones, the process varies depending on the brand and manufacturer.
- Invasive strep: ‘Don’t wait’ to seek care, N.S. woman warns on long road to recovery
- Grocery code: How Ottawa has tried to get Loblaw, Walmart on board
- ‘Super lice’ are becoming more resistant to chemical shampoos. What to use instead
- Canadian food banks are on the brink: ‘This is not a sustainable situation’
WATCH: Why your smartphone is at risk from hackers

Due to several factors however, including limited storage on smartphones and the reduced size of the fingerprint sensor in smartphones, mobile devices are only able to capture partial images of the users’ fingerprints.
Aditi Roy, a post-doctoral researcher who co-authored the report, warns that despite the convenience of mobile fingerprint sensors, users shouldn’t rely on them for sensitive transactions.
“The fingerprint-based authentication system is very convenient from users’ point of view. However, unless it is made more secure to different types of attacks (one of which is described in our research), we should not rely on it fully. Especially, this is true in sensitive work like financial transactions. For example, when mobile banking and credit card payment are conducted on these devices,” she says.
Memon goes on to explain that there are several potential solutions to this problem, but that none have been readily integrated by smartphone vendors yet. Some of these include increasing the size of the sensor or increasing the resolution of the fingerprint itself.
Users can also take precautions by limiting the number of fingerprints they store on their devices, or changing the settings on their device to require the pin to unlock it after a certain amount of time. Memon states that the best way to protect your phone however, is to use a two-factor authentication system requiring both a pin and a fingerprint on certain occasions.
WATCH: Tech: Small smartphone accessories for Android and iPhones

“The pin still remains a solid way to protect the phone. We kind of hear about fingerprints being unique, but that’s really just a small part of it. If you take many small parts, you can match any of them. A lot of the work in biometrics is done with the anticipation of the random attack,” Memon goes on.
The study’s co-authors agree however, that while users don’t need to abandon the fingerprint sensor entirely, they do need to be cautious about how much they rely on it. It looks like we won’t be able to say goodbye to passwords and pins just yet.





Comments