(UPDATE Nov. 30): In a statement to Global News, security researcher Matt Jakubowski said the MP3 files he was able to access on Hello Barbie were not recordings, but default lines the doll says when it can’t connect to the Internet.

While he reiterated warnings that sophisticated hackers could find ways to access the doll, he commended Toy Talk for its security protocols so far.
“Overall I think ToyTalk has done a outstanding job on the security protocols they have in place. The doll when in wifi mode requires a client-side cert to be valid in order to access any of the data, it also limits the data that it can accept thus limiting the attack surface,” Jakubowski said in an email.
“ToyTalk also appears to be using HTTPS for all communications to ensure no eavesdropping of any kind can happen. These are all good levels of security that you don’t typically see in many IoT devices. ToyTalk has certainly taken many of the concerns and has addressed them as best as they could.”
——
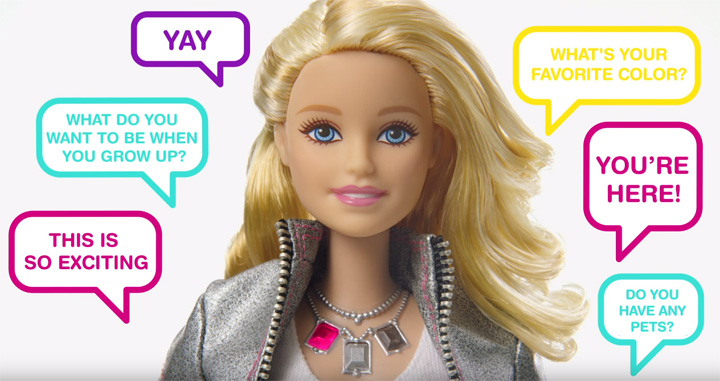
Barbie has had a lot of jobs, but security experts allege her latest gig could be akin to a spy.
The Wi-Fi connected Hello Barbie uses voice recognition software – similar to voice assistant programs like Apple’s Siri or Google Now – to interact with children.
By holding down a button on Barbie’s belt, kids are able to talk to her – their voices are then recorded and sent to the cloud where they are analyzed. Barbie’s software then comes up with an intelligent response, mimicking a real-life conversation.
But U.S. security researcher Matt Jakubowski is warning parents that the doll can be hacked, leaving kids at risk of being spied on.
After hacking Hello Barbie’s software, Jakubowski claims he was able to extract system information, Wi-Fi network names, account IDs for the account the doll was connected to and even MP3 files.
“I was able to get some information out of it that I probably shouldn’t have,” he told NBC Chicago.
More troubling are the researcher’s claims that hackers could eventually find a way to access the doll’s microphone.
“It’s just a matter of time before we are able to replace their servers with ours make her say anything we want,” he said.
However, Toy Talk – which teamed up with Mattel to produce Hello Barbie – has downplayed the severity of Jakubowski’s claims, noting, “no children’s audio was accessed, no passwords were compromised, and no dolls were made to say anything unintended.”
“They opened the doll, de-soldered the chip from the circuit board, and placed the chip into a reader so they can look at the memory. However, this does not give access to sensitive information, by design,” read a statement from Martin Reddy, co-founder of Toy Talk.
“It’s worth noting that if someone were to modify the firmware, the doll will refuse to boot it. Also, this all requires physical access to the internals of a specific doll.”
Global News reached out to Mattel regarding Hello Barbie’s security concerns, but a request for comment was not returned.
This isn’t the first time experts have issued warnings about the interactive doll.
U.S. based organization Campaign for a Commercial-Free Childhood (CCFC) has been lobbying against Hello Barbie since it was announced in February. The child rights group believes the doll violates kid’s privacy by recording and storing conversations and alleges the doll could be used to collect data that marketers can use to unfairly target kids.
In November, the CCFC launched a campaign called “Hell no Barbie,” in an effort to educate parents about the concerns surrounding the doll.
According to Toy Talk’s privacy policy, the company is taking steps to protect kid’s personal information.
“We cannot prevent children from providing personal information when they talk with Hello Barbie, and such information may be captured in the recordings. However, it is our policy to delete such personal information where we become aware of it,” reads the statement.
In response to Jakubowski’s findings, the company also announced it is creating a “bug bounty” program that will reward security researchers for responsibly disclosing security vulnerabilities.





Comments