WATCH: The slew of private photos of celebrities hacked from Apple’s iCloud and leaked online has people asking if anything can be kept private any more. As Jackson Proskow reports, it’s a reminder how we’re all vulnerable online.

TORONTO – Whether you partake in the art of “nude selfies” or not, the recent leak of hundreds of stolen nude celebrity photos might have you concerned about your private data.
It’s believed that nude photos of a-listers, including Jennifer Lawrence, Kirsten Dunst and Kate Upton, were stolen directly from the celebrities’ online accounts – particularly Apple’s iCloud service.
On Tuesday Apple confirmed that certain celebrity accounts were targeted in specific attacks, but denied reports that the leak stemmed from a security flaw in its iCloud services.
READ MORE: Investigators probe leak of 100s of celebrity nude photos
“After more than 40 hours of investigation, we have discovered that certain celebrity accounts were compromised by a very targeted attack on user names, passwords and security questions, a practice that has become all too common on the Internet,” read the company’s statement.
“None of the cases we have investigated has resulted from any breach in any of Apple’s systems including iCloud or Find my iPhone.”
Nevertheless, the massive breach of privacy may have some users of cloud-based storage solutions worried about their data.
The truth is no service is perfect and breaches happen – but the onus lies in the users hand to control what information they trust to the cloud.
“Various services can guarantee different levels of security, but at the end of the day – for 99.9 per cent of individuals – it’s very hard to test or evaluate the claims of the company at fault,” said Chris Parsons, post-doctoral fellow with the Citizen Lab at the Munk School of Global Affairs and cyber security expert.

Get breaking National news
“In terms of highly sensitive material, cloud-based services may not be the best place to store that long term.”
Cloud-based storage can be a lifesaver in instances where your computer crashes and you need to recover lost data, but Parsons suggests that users carefully weigh how they store sensitive information that may be embarrassing or damaging if it fell into someone else’s hands.
READ MORE: Apple denies iCloud security flaw to blame for celebrity photo hack
Sexual images, for example, might be better stored on a USB key locked away in your desk drawer – so long as you don’t have a habit of misplacing things.
But Parsons added that consumer’s lack of knowledge about the cloud may also be to blame.
“People are told that they should be using these services for backup, but the recommendation doesn’t mean that people understand what is really going on,” he said.
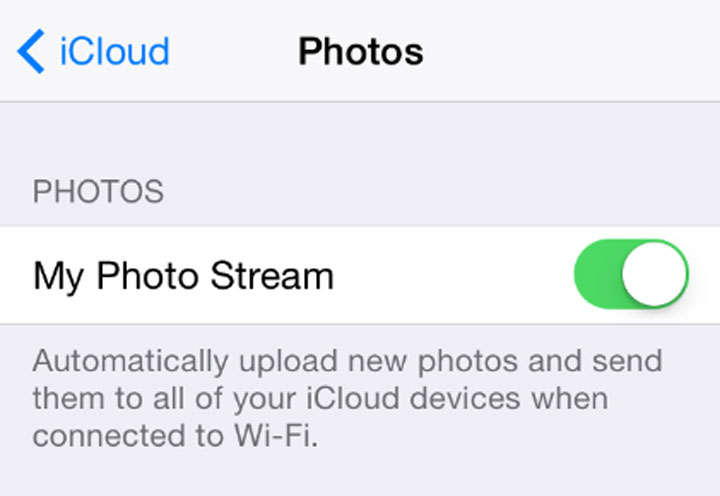
For example, Apple users in particular may not realize that iCloud includes a feature called Photo Stream which automatically backs up the photos taken on their iPhone to the cloud. This may be how attackers gained access to some of the stolen celebrity photos.
To check if your Photo Stream is turned on simply go to “Settings,” then “iCloud,” then scroll down and tap on “Photos.” If Photo Stream is turned on (indicated by the green toggle) that means the photos you take on your iPhone are being backed up to iCloud and shared with other devices attached to that iCloud account.
Simply slide the toggle to the left if you wish to turn it off.
Strong passwords
As with any sort of a security worry, having a strong password can make all the difference. Parsons suggests that users create super long passwords to help ward off potential attacks.
“A long password doesn’t have to be made up of upper and lowercase letter, dashes and other stuff you won’t remember. A series of phrases even works,” said Parsons, who suggested using a sentence for a longer password.
Apple, in particular, requires user passwords to be eight characters long and include an uppercase letter, a lowercase letter and a number.
Users should try to stay away from easy-to-guess passwords like “1,2,3,4″ or “Password” and easy to guess identifiers like your dog’s name. Passwords that use up to ten upper- and lower-case letters mixed with numbers are also proven to be more secure – despite being hard to remember.
One tip is to construct a password from a sentence, mix in a few upper case letters and a number – for example, “There is no place like home,” would become “tiNOplh62.”
READ MORE: How to create a more secure password
Parsons also suggests that users look into a password manager that auto-creates alpha numeric passwords automatically and stores them in the manager.
Apple recently introduced a similar product for iCloud users called iCloud Keychain, which can suggest complicated alpha-numeric passwords for the user and save them in the keychain. iCloud Keychain can also remember credit card and Wi-Fi information.
Enable two-step authentication
In light of the celebrity photo hack, Apple is suggesting concerned users enable two-step authentication on their accounts for peace of mind.
Two-step or two-factor authentication requires the user to input their cellphone number to the service in order to send a text message containing a secondary login every time a login attempt is made.
iCloud users can enable two-factor authentication by going to the “My Apple ID” website, clicking on “Manage my Apple ID,” selecting “Password and Security,” and follow the “Two-step verification” instructions.
Other cloud-based services like Google and DropBox also allow users to enable two-step authentication.







Comments
Want to discuss? Please read our Commenting Policy first.